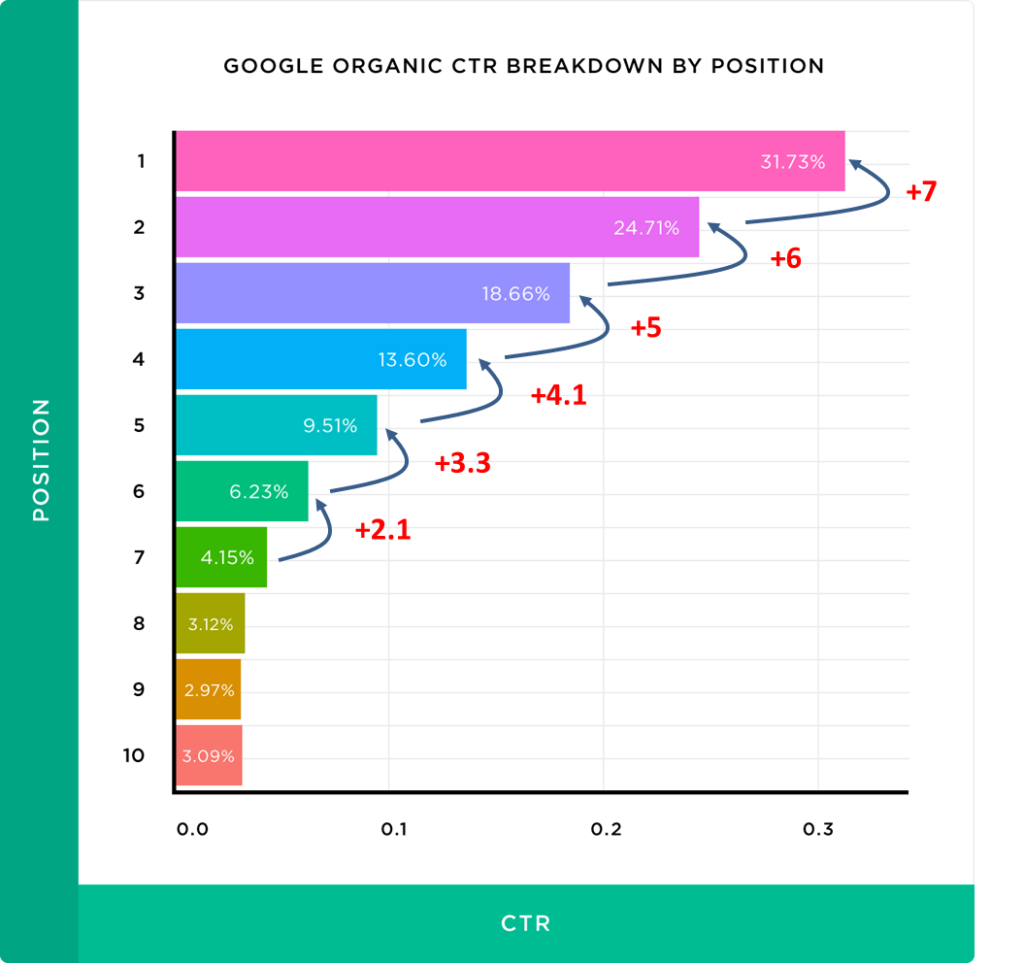
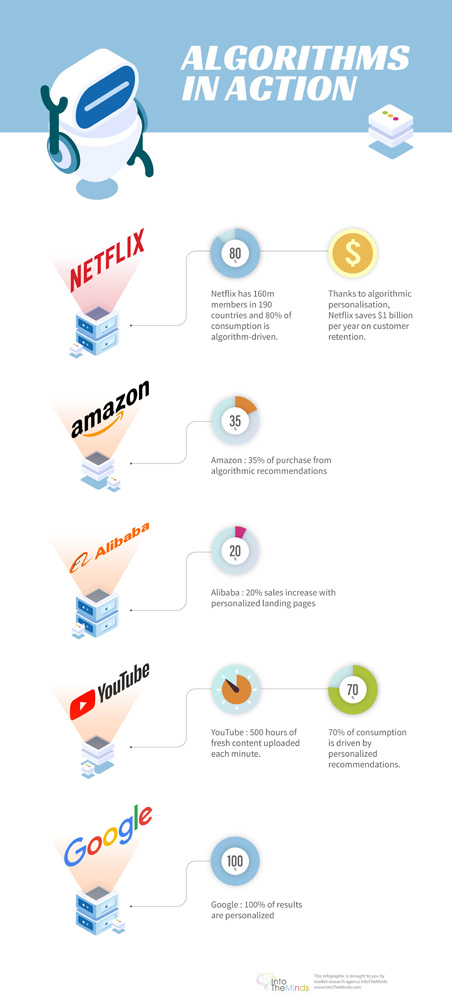
Hacking a recommendation algorithm is an operation that can be very profitable. Indeed, some recommendation algorithms are ubiquitous in our digital life and strongly influence our behaviour. We have become dependent on algorithms without realising it. For example, 35% of purchases on Amazon are the direct consequence of an algorithmic recommendation. An algorithm suggests 80 % of movies watched on Netflix and 75% of videos on YouTube. Pagerank, Google’s algorithm, is probably the most studied recommendation algorithm, the one that is the subject of the most “hacking” attempts because it has a significant economic impact. More than 70% of clicks go to the first three positions in Google.
But apart from Google, it must be admitted that algorithm hacking is a subject that has been largely neglected. We noticed it during the last RecSys conference. However, as Simon Weckert’s project shows, hacking an algorithm is possible (see the video below). And what is astonishing is that it is even relatively “easy” when one intervenes at an early stage. The secret of algorithm manipulation lies in sending false information to the algorithm, and this technique is very complicated to prevent.
Summary
What do you need to do to fool a recommendation algorithm?
Most algorithms that recommend content, use the same rules to work, the corresponding data to “feed”:
one or more engagement metrics (likes, comments, number of shares)
the velocity (that is to say, the speed with which content engages those who have seen it)
site-specific metrics (viewing in the case of a video website like YouTube, paying a sum of money to support a project in the case of Kickstarter)
Once you have understood this, you can manipulate the algorithm. Just send information to the algorithm that will disrupt its performance and lead to a successful outcome in the desired direction. The effects are guaranteed, in the short term anyway.
Hacking recommendation algorithms: what are the consequences?
The consequences can be significant, and not only financially.
We won’t go back to Google’s algorithm. The introduction of this article will give you a good overview of the consequences. I will provide you with these only in the form of a graph below.
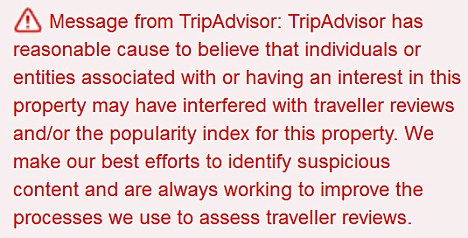
TripAdvisor
The TripAdvisor algorithm works based on passenger ratings. Hacking the algorithm is therefore equivalent to multiplying the number of complimentary comments, even if it means inventing them. It is this that led TripAdvisor to punish La Mère Poulard, a seemingly banal restaurant located in a very touristy place: Mont-Saint-Michel. The phenomenon of false reviews is such that TripAdvisor has put in place a “red badge” that warns visitors of the probable existence of fake comments on a particular profile. The DGCCRF (the department for the repression of fraud in France) estimates that 45% of the online reviews are false.
Kickstarter
Seeing his crowdfunding campaign posted among the top 10 most popular on Kickstarter’s homepage inevitably attracts visitors and increases the chances of his project being funded. Hackers have, therefore, specialised in manipulating Kickstarter’s algorithm. They use private groups to generate a substantial commitment in a short period, which allows having a high velocity, a high engagement, and to be quickly at the top of the highlighted campaigns. The only problem is keeping that position. Indeed, this “mass effect” has only a limited impact in time, and it is, therefore, necessary to be able to mobilise increasingly higher audiences (notably by spending high advertising budgets) to guarantee its position at the top of the ranking.
The operation of the LinkedIn algorithm is quite well known. The overall workings of the algorithm have been explained by Pete Davis here, but he has not revealed how to “manipulate” the algorithm, of course. It appears that a determining criterion in the ability of a post to reach a broad audience is its velocity. That is to say that the post in question must generate engagement (likes, comments, shares) quickly. As an indication, a maximum of reactions should be ensured within the first hour following publication. I interviewed a LinkedIn expert, Bruno Fridlansky, to give us his tips and tricks for making your LinkedIn posts go viral.
The three golden rules for a popular post on LinkedIn
For your LinkedIn post to reach a significant audience (beyond your 2nd circle), the LinkedIn algorithm must receive the following signals:
- a maximum of comments within the first hour of publication
- respond to each comment within 2 hours
- no hyperlink in the post
Interview: Bruno Fridlansky’s advice to increase the virality of your LinkedIn posts.
What are the levers you need to play with to take advantage of the LinkedIn algorithm?
“Today, what measures commitment…is the feedback we receive on our publications and the author’s response to the feedback. So, is there a good hour to publish? No, there’s no more bullshit than those infographics that come out with hourly averages. If we have to respect them, that is to say; we have to publish on Tuesday, Thursday, between 10 and 11 am. It’s just averages, and averages mean nothing. I say that the right time to publish is when you know that you can be available within two hours to respond to comments because it is a tool for making conversations. If you want to communicate, it’s useless. You’re not going to make any connections. The purpose of this tool is to connect with humans and make professional relationships. So, you’re going to publish when you know you’re going to be able to respond to the people who are going to comment on you back there. What is a good publication? There, indeed, the format can play a role. What does that mean? LinkedIn will favour publications with text or text, with a PDF document or a native video, that is to say, a video that you will upload directly to LinkedIn. On the other hand, it will rather penalise publications with external links. It makes LinkedIn members leave, and that’s out of the question for the network. They want members to stay within LinkedIn. That’s on the format. Then what do you say if you’re talking about yourself? What I very vulgarly call Professional Wanking, interests no one, except your small ecosystems. But at that moment, we are among ourselves. No, what is needed is to bring value. What are you going to publish that will bring value to your interlocutor? How are you going to make them learn something? Make him or her progress? Make them think and then think together through the comments that will interact. Don’t tell me about you, tell me about me. That’s all that interests me. That’s how everybody reacts.”
The right time to publish is when you know you can be available in the next two hours.
Google Maps
In a previous article, we have already talked about the experiment carried out by Simon Weckert, a German artist who “hacked” Google Maps to make it appear as though there was a traffic jam on a Berlin street. The consequences can be significant because by artificially creating a traffic jam, it becomes possible to divert car traffic and to favour/disadvantage certain businesses. McDonald’s has carried out a more significant scale experiment in California, which mixed advertising on Waze with traditional billboards to bring customers to its points of sale.
To conclude
Algorithms govern our lives. It is impossible to move in the digital world without being in contact with an algorithm, in particular a recommendation algorithm. Whether we are making a purchase on Amazon (35% of sales) or watching a video on Netflix (80% of videos watched), algorithms advise us, and we follow (often blindly) their prescriptions. The algorithms can, therefore, manipulate us.
The designers of these computer programs swear by their great Gods that the algorithms are objective. They probably are to some extent. But the techniques we have seen in this article are a completely different way of hacking since they are false signals that are sent to the algorithm in order to deceive it. The algorithm, therefore, shows no sign of malfunctioning but reacts as expected to the stimuli sent to it. It will be remembered that Google’s algorithm had been “hacked” in the same way by those who created “link farms”. This “hyperlink fraud” had been detected, and the algorithm improved. Still, fraudsters are always one step ahead, and it will never be possible to predict, in advance, all possible hijackings of an algorithm.